Recently updated on September 23, 2025
American Financial Sector gets cyber attacked “over a billion times a year,” stated CEO of PayPal and a chairman of Symantec, Dan Schulman. The number of data breaches rose immensely – in the second quarter of 2025 a staggering 94 million data records were exposed in breaches, affecting millions of people across the globe.
There is nothing extraordinary about those numbers: the bigger the Fintech industry becomes, the bigger security threats it faces. There is no reason for worry, though: you just have to ensure that your Fintech application is developed with relevant security practices to minimize the probability of breaches.
Why Security Matters in Fintech Apps
Fintech companies should pay careful attention to their cybersecurity and aim for the development of secure fintech applications for a couple of different reasons:
Financial Data Protection
Fintech companies deal with sensitive financial information, including personal and account details, payment data, and transaction histories. Preventing cyberattacks is essential to safeguard this data from theft and fraud, which could lead to financial losses and reputational damage.
Customer Trust and User Confidence
Fintech businesses rely on the trust of their customers. If a breach occurs and customer data is compromised, it can erode trust and result in customer churn. Maintaining a strong security posture is critical to retaining customer confidence.
Financial Stability and Fraud Prevention
A successful cyberattack can disrupt fintech operations, impacting the availability of services, transaction processing, and overall financial stability. This can result in significant financial losses and damage a fintech company’s reputation.
Competitive Advantage in the Market
Security can be a competitive differentiator. Fintech companies that invest in app security can use it as a selling point to attract security-conscious customers and partners.
Legal Liabilities and Compliance Risks
In a data breach, fintech companies may face legal liabilities, including lawsuits from affected customers, partners, or regulators. Preventing cyberattacks can reduce the risk of legal consequences.
A key for fintech security app development is that you and your developers should follow industry best practices for application security, conduct regular security assessments and testing, implement strong encryption, use secure coding practices, and have a well-defined incident response plan. By prioritizing security from the outset, your company can reduce the risk of data breaches and other security-related issues, ultimately ensuring the safety and trust of your users.
Key Challenges for Fintech App Security
Securing fintech apps comes with its own challenges, as they deal with sensitive financial information and are prime targets for cybercriminals. So before we discover how to develop a secure fintech app, let’s take a look at some of the most common challenges that may appear:
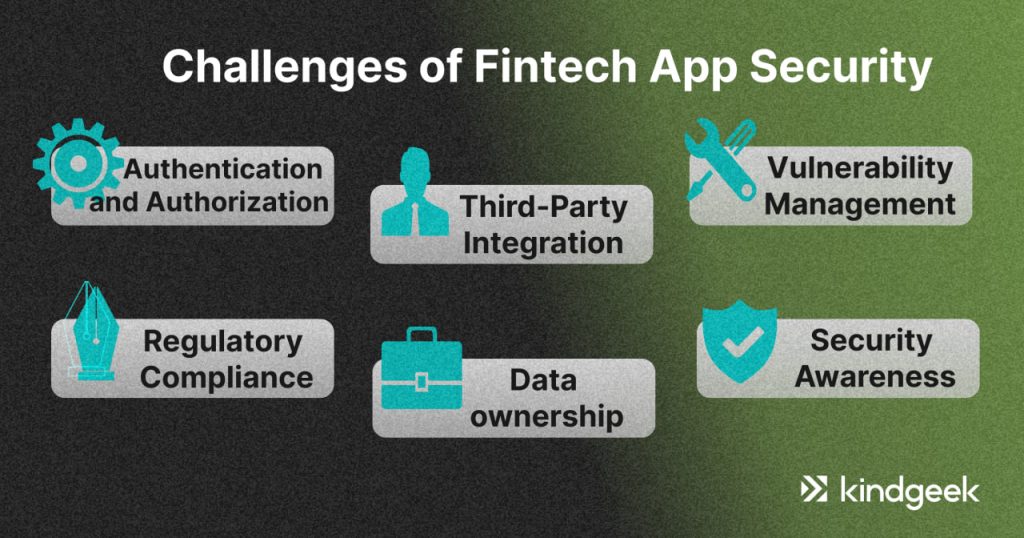
Authentication and Authorization Risks
Securely managing user access and permissions is essential. The challenge is implementing robust authentication methods, such as multi-factor authentication while ensuring that users have the appropriate levels of access to the app’s features and data.
Third-Party Integration Vulnerabilities
Fintech apps often rely on third-party APIs and services for various functions, like payment processing or identity verification. Integrating these services securely while maintaining control over potential vulnerabilities is a challenge.
Effective Vulnerability Management
Hackers can exploit system weaknesses to access sensitive information. Identifying and addressing software vulnerabilities and patches promptly is crucial. This requires continuous monitoring and assessment of the app’s code and dependencies.
Meeting Regulatory Compliance Standards
Fintech apps must adhere to various financial and data protection regulations. The challenge is in staying updated with evolving regulations and ensuring compliance, which often requires significant resources and expertise.
Data Ownership and Privacy Issues
Fintech companies need effective mechanisms and procedures for regulating who can access, create, modify, and delete their data. Data ownership requires the knowledge of multiple technical and legal processes.
Security Awareness Among Employees and Users
Ensuring the entire organization, from developers to non-technical staff, is security-aware and follows best practices. This challenge also includes educating users about security best practices, such as password hygiene and recognizing phishing attempts, which is essential but can take time to implement effectively.
To address these challenges, fintech companies should follow fintech app security best practices, invest in robust security practices, conduct regular security audits and testing, and stay informed about emerging threats.
7 Best Practices for Secure Fintech App Development
Developing a secure app requires a thorough and proactive approach to security. Here are some tips for fintech security app development:

Implementing Secure Authentication and Authorization
The most typical indication of security vulnerability is a lack of authentication and appropriate identifiable measures. Fintech apps need to be sure of the fact that cybercriminals are not able to access personal details through misrepresentation.
Here are some of the best practices for authentication and authorization:
- Encourage users to create strong passwords with upper and lower-case letters, numbers, and special characters.
- Enable multi-factor authentication to add an extra layer of security. This can include something the user knows (password) and something they have (a mobile device or hardware token).
- Implement rate limiting to prevent brute-force attacks by limiting the number of login attempts within a specified time period.
- Implement Role-Based Access Control (RBAC) to assign specific roles (e.g., user, administrator, manager) to users, each with a predefined set of permissions.
- Users should be granted the minimum level of access necessary to perform their tasks. Avoid giving users excessive permissions.
- Ensure that APIs used by the app enforce proper authorization controls to prevent unauthorized access to data and functionality.
Addressing the Human Factor in Security
Remember the human factor. Companies “are three times more likely to be breached via social attacks than technical failures.” It makes a person the weakest spot of any piece of software.
So, even if you have reason to believe that your software is protected better than Fort Knox, remember to educate employees on cybersecurity, conduct security awareness training, and remind them about the possible threats by any means necessary.
Writing and Maintaining Reliable, Secure Code
Program code is a foundation of security. Code is the blood of the enterprise software development, and regardless of the programming language, there are standard practices that help ensure the blood has its lymphocytes. These standard practices that help to build reliable project logic include:
1) Educating oneself on secure coding helps avoid prevalent defects, bugs, and logic flaws within the code. In addition, it is essential to learn what patterns that may compromise security to prevent.
2) Including input validation to check any data received from other sources to prevent malicious code injection into a project.
3) Not writing unnecessarily complicated algorithms as they may lead to gaps in a project’s protection, which are difficult to notice and increase the possibility of bugs.
4) Ensuring that a project sends the minimum required data to external sources to prevent leaking of sensitive information.
A bright example of an unintentional mistake in a project’s logic, which might have caused a disaster if a person with criminal intentions figured it out, is a Fiserv case. Fiserv is a global provider of financial services technology, which reported a total revenue of $5.5 billion in 2016 and is often a member of the Fortune “World’s Most Admired Companies” list.
One day, a security researcher, Kristian Erik Hansen, reported that he discovered an issue while logging into an account of a small bank.
Hermansen had signed up to get email alerts any time a new transaction was posted to his account, and he noticed the site assigned his alert a specific “event number.” Working on a hunch that these event numbers might be assigned sequentially and that other records might be available if requested directly, Hermansen requested the same page again but first edited the site’s code in his browser so that his event number was decremented by one digit.
In an instant, he could then view and edit alerts previously set up by another bank customer and could see that customer’s email address, phone number, and total bank account number.
A person with technical knowledge and bad intentions could have exploited this breach to add and delete phone numbers or emails to receive alerts about transactions and generally monitor the transaction activity of the bank users. This security issue was shut down in time, and the probable business disaster was avoided, while people received a valuable lesson on cybersecurity.
Enhancing Customer Awareness of Security Best Practices
One of the main tasks of the development team is to ensure that a user has everything to secure personal information and that their actions or lack of knowledge will not compromise the security of the app.
Therefore:
1) An app should monitor all the activity of a user to notice any unusual actions, such as unusual times of performed action, frequent actions, actions with a big sum of money, or actions performed from unusual locations. If there is a strange activity, request additional authenticatioт or block this activity.
2) Ensure an application does not save a password and log in. It is frustrating to input login and password each time, but it is essential for security.
5) Inform your users regarding the important aspects of their security. Tell them how they need to act in case they lose a phone, how they can block their account, remind them to change a password in case of a strange activity, and remind them that it is dangerous to use an application via public wifi networks.
Developing Secure and Well-Monitored APIs
API security is a critical aspect of fintech app security, as vulnerabilities or weaknesses in API implementations can have far-reaching consequences, including data breaches and financial losses. By following these best practices and continuously monitoring and updating your API security measures, you can significantly reduce the risk of security incidents and protect your fintech app’s users and data:
- Like user authentication, APIs should employ strong authentication and authorization mechanisms to ensure only authorized users or applications can access the API. Implement OAuth or API keys for secure access control.
- Implement rate limiting to prevent abuse or overload of your API. This can help protect the system from DDoS attacks and ensure the API remains responsive to legitimate requests.
- Implement strict access controls to determine who can access specific API endpoints and what actions they can perform. Apply the principle of least privilege to grant minimum necessary access.
- Design proper error-handling mechanisms for your API. Avoid revealing sensitive information in error messages and return generic error responses to external clients.
- Regularly test your API for vulnerabilities, including security scans, penetration testing, and code reviews. This helps identify and remediate security flaws and weaknesses.
Utilizing Strong Data Encryption Methods
When data is being sent from one device to another, it is relatively easy to steal. Therefore, it is important to encrypt data and transform it into a mess that only the receiving side can decipher. There are various approaches to do this. The primary task of the developers is to choose the most relevant and reliable method of encryption that will suit them best.
If you are looking for some ways to improve fintech app security, make sure you follow all of the best practices mentioned above. Here is also a shorter list of security features that your fintech app should have:
- Strong Authentication: Implement multi-factor authentication (MFA) to enhance user authentication. MFA requires users to provide two or more verification factors, such as a password and a one-time code from a mobile app, for added security.
- Secure Password Policies: Enforce strong password policies for user accounts. Encourage users to create complex passwords and regularly update them.
- Access Control: Implement role-based access control (RBAC) to determine what features and data each user can access based on their role or permissions.
- API Security: Secure APIs used by the app with proper authentication and access controls. Limit API access to authorized users and applications.
- User Education: Provide users with security education and awareness materials to help them recognize common threats like phishing and maintain secure practices.
- Regulatory Compliance: Ensure your app complies with relevant financial regulations and data protection laws in the regions where it operates.
- Cloud Security: If your app uses cloud services, apply secure cloud practices, including encryption, IAM, and secure configurations.
- Security Testing: Regularly perform security testing, including vulnerability assessments and penetration testing, to identify and remediate security weaknesses.
Establish Incident Response and Risk Management
Even with robust security, no fintech app is immune to threats. A well-prepared incident response and risk management framework ensures resilience and business continuity.
- Incident Response Plan: Define clear roles, responsibilities, and escalation paths for handling security breaches. This includes detection, containment, eradication, recovery, and post-incident review.
- Continuous Monitoring: Deploy SIEM (Security Information and Event Management) tools to centralize logs, detect anomalies, and speed up incident identification.
- Regular Risk Assessments: Perform vulnerability scans, penetration tests, and third-party risk reviews to identify weaknesses before attackers do.
- Data Backup and Recovery: Ensure that critical financial and user data is backed up securely and that recovery protocols are tested regularly.
- Regulatory Compliance: Align risk management practices with financial regulations (e.g., PCI DSS, GDPR, PSD2) to avoid penalties and maintain user trust.
- Training and Awareness: Equip your development and operations teams with knowledge to recognize threats and respond quickly to minimize impact.
A mature incident response and risk management approach turns security from a defensive measure into a competitive advantage—boosting user trust and reducing downtime.
Consider Kindgeek Your Trusted Partner
If you are looking to develop a secure fintech application, consider Kindgeek. We are a full-cycle fintech development company that provides core fintech banking and payment solutions to serve as a software shortcut for businesses looking to launch their fintech products.
Our white-label fintech solution can greatly speed up your way to the market. With a wide range of pre-built features, combined with thoughtful customization and development, you receive a solution with the functionality to jumpstart your online finance business or get digital without heavy upfront investment.
We also provide a white-label digital banking platform, which serves as a foundation for digital finance products. The customizable white-label core allows you to build on top of it and create a unique customer experience. There is no need to start from scratch – go to market quickly and cost-effectively.
Looking to supercharge your product with AI features or streamline existing business workflows? Check out our AI assistant services, AI transformation services or a comprehensive AI automation platform to unleash the full potential of artificial intelligence for your business.
Feeling a bit overwhelmed and don’t know where to start?
Contact us and have a brief talk with our experts to learn how we can support your unique needs.
Conclusion
Security features and tips for fintech app security solutions that are mentioned in this article are essential for fintech apps to protect sensitive financial data, maintain user trust, and ensure regulatory compliance. Collaborating with cybersecurity experts and organizations is beneficial to address security challenges effectively.
We wrote quite a bit of text, but a single sentence can underline all of the mentioned above:
“Work with an experienced Software Development team.”
It does not matter whether you outsource the development or work with an in-house team; if you want to create a Fintech product, you want to be sure that all stakeholders are equipped to develop a digital Fort Knox.
What are security best practices for fintech application development?
Recently updated on April 18, 2024
The best practices for the secure fintech app are building a reliable code, secure authentication, and authorization processes, data encryption, secure APIs, customer awareness, understanding the role of human factors, and others.
What security features must a fintech app have to prevent hacking?
Recently updated on April 18, 2024
A secure fintech app should have the following features: strong authentication, secure password policies, access control, API security, user education, regulatory compliance, cloud security, security testing, and others.
Why is it important to invest in fintech app security?
Recently updated on April 18, 2024
You should follow best practices for application security, conduct regular security assessments, implement strong encryption, and use secure coding practices. By prioritizing security, your company can reduce the risk of data breaches and other security-related issues, ultimately ensuring the safety and trust of your users.


